Featured
Table of Contents
- – Vpn Protocols - Secure Internet Browsing - Priv...
- – How Do Vpns Work? Vpn Encryption & Tunneling E...
- – Vpn Tunnels Explained: What Are They And How C...
- – What Does A Vpn Tunnel Do
- – Vpn Tunnels Explained: What Are They And How ...
- – Guide To Vpn Protocols: Using Vpns Securely ...
- – Common Types Of Vpn Tunneling Protocol
- – Virtual Private Network (Vpn) Tunneling Prot...
- – What Is A Vpn And How Does It Work?
- – What Is A Vpn Tunnel And How Does It Work?
Vpn Protocols - Secure Internet Browsing - Privatevpn
This provides more versatility than producing an SSH tunnel to a single port as formerly described. SOCKS can free the user from the constraints of connecting only to a predefined remote port and server. If an application does not support SOCKS, a proxifier can be utilized to reroute the application to the local SOCKS proxy server.
This creates tun (layer 3, default) or tap (layer 2) virtual user interfaces on both ends of the connection. This enables typical network management and routing to be used, and when used on routers, the traffic for an entire subnetwork can be tunneled.
How Do Vpns Work? Vpn Encryption & Tunneling Explained
VPNs can deal with any gadget that links to the internet and can run a VPN app, including your mobile phone, computer, and some wise TVs. All you need to do is download a VPN app to your device and follow the instructions to connect to a VPN server. When you connect to the VPN server, an encrypted connection is negotiated between your device and the VPN server.
In the last 20 years, mass surveillance has been released versus whole populations in lots of countries.
Vpn Tunnels Explained: What Are They And How Can ...
This leaves your traffic vulnerable to interception, including any passwords or other sensitive information you enter. A larger concern is that the data collected from you by any of the above trackers will suffer a data leak that exposes your details. A VPN will not prevent all (and even most) leaks, however it is one more layer of security in an information space designed to extract your information.
Lots of streaming websites are not accessible in certain countries. If you're taking a trip abroad, you can link to a VPN server back home to log in to your account. Proton VPN users can access lots of popular streaming websites by linking to a Plus server because country. There are other benefits of a VPN that are very important in particular usage cases: Avoid peers from seeing your genuine IP address when utilizing P2P file sharing (Bit, Gush).
What Does A Vpn Tunnel Do
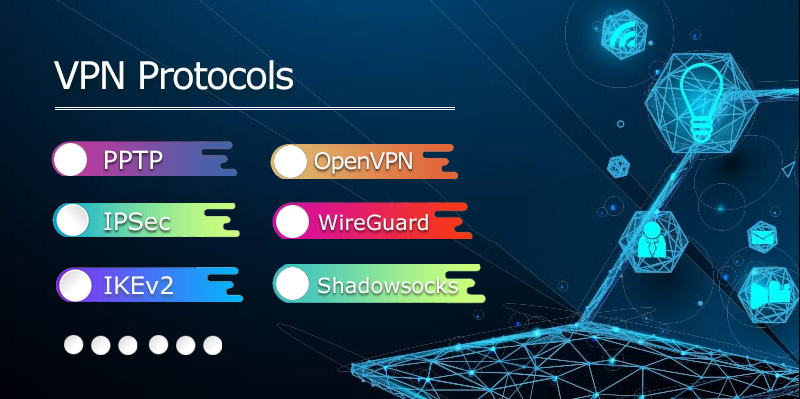
The protocols are essentially a set of guidelines the computers must follow to develop the encrypted connection, maintain it, and send your web traffic inside it. VPN procedures have different strengths and weak points. Some are faster or slower, more steady or less stable, or more resistant to attacks. Here's a fast overview: An older VPN protocol with numerous known vulnerabilities.
Layer two tunneling protocol (L2TP) and Internet Procedure security (IPSec) are two procedures that typically collaborate to negotiate the server connection and handle the encryption, respectively. This is a more safe system than PPTP, but it might have vulnerabilities and usually isn't as fast or steady as more recent protocols.
Vpn Tunnels Explained: What Are They And How Can ...
A VPN tunnel is simply a metaphor for the file encryption a VPN utilizes to hide your information as it takes a trip in between your gadget and the VPN server. The majority of web traffic shows up to others on the network, so third celebrations, like your web service provider or government agencies, can see what sites you go to and where you are located.
VPN tunneling likewise prevents hackers from misusing data by encrypting them from end to end. Most VPNs use AES-256 encryption, which militaries, banks, and federal governments utilize to secure personal data. It is technically difficult to break the AES-256 file encryption without a cipher key, as it would take trillions of years to do so.
Guide To Vpn Protocols: Using Vpns Securely In 2023
Like IKe, V2, Open, VPN provides formidable speed and security for VPN tunneling. It is also open source, which means experts have continually vetted and enhanced the protocol for many years. Wire, Guard is the most current and most safe VPN file encryption protocol. Compared to Open, VPN and IKEv2, Wireguard is much faster and more safe, thanks to its smaller sized code size.
Proxies just work for browsers and not apps. If you use an app regardless of linking to the proxy, your real IP address will still be revealed.
Common Types Of Vpn Tunneling Protocol

VPN technology is not intricate, but there are. All of this can get extremely technical, so here's a fast rundown of which types of VPN and tunneling protocols are best for your business.
Organizations primarily use this type to. You can think of it as a VPN connection making a secure path from your device to access sensitive files or company products on the other end.
Virtual Private Network (Vpn) Tunneling Protocols
Many companies embrace widely hosted elsewhere, utilizing enormous data centers. For that reason, setting remote gain access to VPN up may not be the most practical option as in those cases, the data would be going from users' device to the central hub, to the information center and back. So not only this might introduce.
Though, it's worth noting that you ought to prepare depending on the variety of users accessing them. The more of them you'll have, the more capable hardware you'll require. is to produce a unified network that is always on. It needs individually setting up for both networks, and it works finest for cases when you have numerous remote websites.
What Is A Vpn And How Does It Work?
It supplies detailed guidelines on packaging the data and what checks to perform when it reaches its destination. These various methods. Here are the most popular ones. is a VPN tunneling procedure that protects information exchange by. It is twofold encryption the encrypted message beings in the information package, which is additional encrypted once again.
There even are exclusive Wire, Guard implementations like Nord, Lynx. A VPN procedure must be the last thing off the list that you must be picking. : remote access or site-to-site. It needs to limit your list of alternatives. Though, it deserves keeping in mind that neither remote access nor site-to-site are the only possibilities to establish an Internet-based VPN.
What Is A Vpn Tunnel And How Does It Work?
I.e., if you're already utilizing routers that natively support Open, VPN, it might make more sense to use them instead of tossing them out to get ones that can manage Wireguard.
What is a VPN Tunnel & How VPN Tunneling Functions? Data, Prot is supported by its audience. As we browse the web, we leave crumbs of searching information on the pages we visit.
Table of Contents
- – Vpn Protocols - Secure Internet Browsing - Priv...
- – How Do Vpns Work? Vpn Encryption & Tunneling E...
- – Vpn Tunnels Explained: What Are They And How C...
- – What Does A Vpn Tunnel Do
- – Vpn Tunnels Explained: What Are They And How ...
- – Guide To Vpn Protocols: Using Vpns Securely ...
- – Common Types Of Vpn Tunneling Protocol
- – Virtual Private Network (Vpn) Tunneling Prot...
- – What Is A Vpn And How Does It Work?
- – What Is A Vpn Tunnel And How Does It Work?
Latest Posts
Best Vpns For Small Businesses (2023) - Bestvpn.org
8 Best Vpns For Android In 2023: Fast & Easy To Use
15 Best Vpn Services Of 2023 (Updated: May 30)
More
Latest Posts
Best Vpns For Small Businesses (2023) - Bestvpn.org
8 Best Vpns For Android In 2023: Fast & Easy To Use
15 Best Vpn Services Of 2023 (Updated: May 30)